Introduction
Open source software, out-sourcing software development and contract programmers pose intellectual property theft exposure for companies today.
More brick-and-mortar corporations are investing heavily in I.T. In-house software development teams come with additional responsibility and risk for the leaders. As more and more software products use component-based technologies there is an increased chance of using open-source products without understanding their licenses.
Consultants and contract workers are hired for software development projects in addition to permanent employees to reduce time to market. Software development work is outsourced to other countries to cut I.T. spending. All these strategies have once common negative aspect – violation of intellectual property rights and subsequent legal action.
In this paper, I explore these three strategies in brief detail and determine the risk and exposure relative to intellectual property violations.
Intellectual Property Issues in the I.T. Department
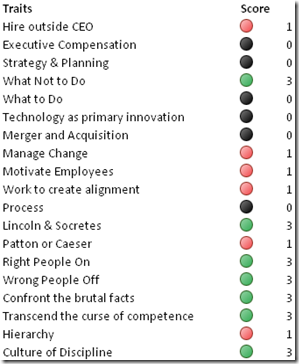
According to independent research conducted by Forrester, CIOs of $ 1 billion-plus companies cite “Intellectual Property Theft” as the type of IT security incident that poses “the most threat” to their company’s business (see Figure 1). Four out of ten CIOs don’t think they spend enough on the most important security threat. Although malicious code and intellectual property theft pose 60% of all risk, and 70% of CIO’s approve IT budgets – yet 40% think not enough is spent on security.

Most often the core differentiator of companies is its business processes, strategic information systems, and technology. Outsourcing forces the company to reveal its internal business processes to vendors. Certain companies do not have strict intellectual property laws. Forrester’s Stephanie warns “North American and European companies should not consider China a viable location for software development and maintenance support. The market is too immature, and the problems associated with this immaturity - a lack of English language skills, the legal and regulatory environment and lack of intellectual property laws - make China too risky today.”
Often open source software is used by IT teams to build software products. Several software frameworks are available to be downloaded for free. What several companies, architects, developers and programmers fail to comprehend is that open source is not the same as “free”. Open source software is licensed. However, most open source license types like Berkeley Software Distribution, Free Software Foundation, or General Public Licenses lack indemnification.
The “as-is” aspect of open source software is risky. There is a possibility that part of open source software “copied code” from some other licensed product. It is very difficult for the companies to identify or compare open source with licensed software products to identify theft. This exposes the company using open source software to lawsuits from companies claiming that the open source software violates their intellectual property rights.
(Figure 1)
Contract workers often are hired for short stints to work on software development and testing. This type of work needs full developer-access privileges on the source code. The obvious risk is to the code being stolen or exposed to others.
Three Regimes that protect IP
Trade secret classification, copyright and patents serve to protect intellectual property under law. In addition, compliance requirements of law such as Sarbanes-Oxley, Gramm-Leach-Bliley and HIPAA are driving software development shops to protect intellectual property, ensure privacy, and aim for correctness in development products and practices.
With time, Trade Secret laws are being tightened. Trade secret plaintiffs sometimes would couch their claims under other, alternative titles, such as "common law misappropriation," "unfair competition," or "breach of confidence." The tactic was often a deliberate ploy to avoid complying with state Uniform Trade Secrets Act [UTSA] statutes. California is the first state that pre-empts such attempts. As more states follow suits, trade secrets laws will be more and more effective.
1998 Digital Millennium Copyright Act that amended the copy-right statute, defeating any technological control that controls access to a computer program in order to make even a legitimate backup copy is infringement. Computer games almost always have copy protection built in, and defeating the controls would be infringement. DVDs are encrypted, another type of technological control.
Challenges to Intellectual Property by the Internet and Technology
Technology is an enabler for both innovation and crime. Companies spend millions in research, design and development. All this information is stored digitally in software files. These portable electronic files make theft easy. Software files can be copied to Floppy disks, CD-RW disks, memory sticks, or other digital RW media and sneaked out of facilities.
Files can be uploaded to web-sites or e-mails from a secure machine to the Internet. Worse, it is possible to install “spy-ware” that can regularly scan machines and upload files automatically.
Websites can screen-scrape or use portal technologies to “grab” published web-pages from other websites and present them as their own. Website mirrors can be created which give access to content of other protected websites.
Hardware theft can result in the same effect. A knowledge worker’s laptop containing critical engineering designs can be invaluable to the knowledge thief. CEOs have the greatest fear of loosing their PDA or laptops.
Conclusion
Although protection of intellectual property is a key issue in the United States, a challenge in the future will be to ensure the same standards across nations. The Patent Cooperation Treaty is a first step in that direction, while it is gaining support in developing nations, like Oman, it is yet to be seen as an effective measure against software piracy and intellectual property theft.
While laws and precaution protect intellectual property, the threat of exposure will continue to increase with technological advances. The proper use of technology is closely related to the ethical and social constituent of nations. At the core of the problem are people and their honesty and integrity. As long as money governs societal well-being, human greed for money will bulldoze over anything that comes in its way – including intellectual property rights.
Reference:
- Moore, Stephanie: Planning Assumption IT Trends 2004: Offshore Outsourcing. Forrester Research Report. (December 2003)
- Laura Koetzle with Charles Rutstein, Angela Tseng, Robert Whiteley. How Much Security Is Enough? Forrester Research Report.(August 2003)
- Nikos Drakos, Alexa Bona. Questions and Answers on Open-Source Licensing. Gartner Research. (October 2002)
- Vijayan, Jaikumar. Security Expectations, Response Rise in India. Computer World, Vol 38, No. 5. (August 30, 2004).
- Graves, Tait. A Trade Secret By Any Other Name is Still a Trade Secret The Intellectual Property Strategist. April 7, 2004, NEWS; Vol. 10; No. 7; Pg. 3
- National Commission on New Technological Uses of Copyrighted Works. Making backup copies violates law. Information Outlook, July 2004 v8 i7 p32(2)
- Business News Publishing. Patent Cooperation Treaty Oman joins the treaty. (2001)